Address Poisoning Attacks Are Rising on Ethereum
A few weeks ago, an Etherscan user, Nima, shared an unpleasant experience after receiving more than 89 Address Watch Alert emails shortly after making just two stablecoin transfers.

As Nima noted, these alerts were triggered by address poisoning transactions created purely to insert lookalike addresses into the wallet’s transaction history. The main goal is to trick users into copying the wrong address when making their next transfer.
Address poisoning has existed on Ethereum for several years. But incidents like this highlight how automated and high-volume these campaigns have become. What used to be occasional spam can now be executed at scale, often inserting poison transfers within minutes of a legitimate transaction.
To understand why these attacks appear more widespread today, it helps to look at two things: how address poisoning campaigns have evolved, and why they are so easy to run at scale.
We also highlight one simple rule to remember to help protect yourself against these attacks.
1) Address Poisoning Has Become Industrialized
Address poisoning was once viewed as a niche trick used by opportunistic attackers. Today, it increasingly resembles an industrialized operation.
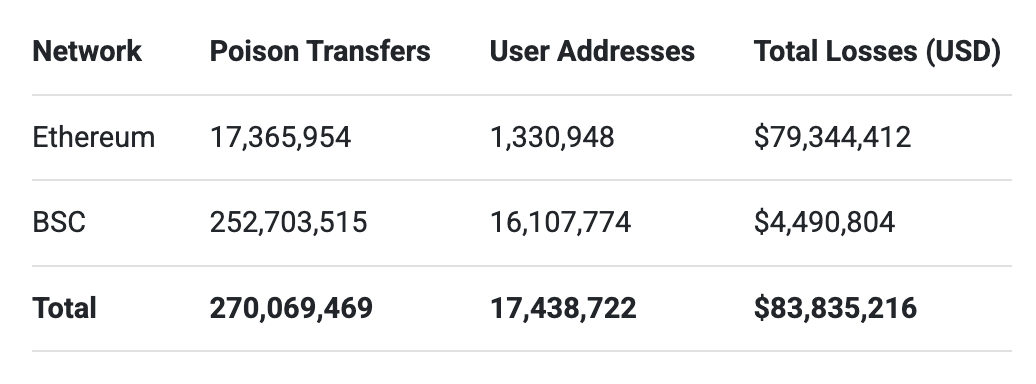
A 2025 study analyzing address poisoning activity between July 2022 and June 2024, before the Fusaka upgrade, identified roughly 17 million poisoning attempts targeting about 1.3 million users on Ethereum, with confirmed losses of at least $79.3 million.
The table below illustrates the scale of address poisoning activity across Ethereum and BSC between July 2022 and June 2024, based on findings from the Blockchain Address Poisoning study. On chains like BSC, where transaction fees are significantly lower, poison transfers occur 1,355% more frequently.
Attackers often monitor blockchain activity to identify potential targets. Once a transaction is detected, automated systems generate lookalike addresses that mimic the beginning and ending characters of legitimate addresses the user has interacted with. Poison transfers are then sent to the target address so the spoofed address appears in the transaction history.
Potential targets are addresses that are more likely to be profitable for attackers. Addresses that make frequent transfers, hold significant token balances, or involved in large transfers tend to receive more poisoning attempts.
Competition Drives Efficiency
One surprising insight from the 2025 research is that different attack groups often compete with one another. In many poisoning campaigns, multiple attackers send poison transfers to the same address at roughly the same time.
Each attacker attempts to insert their lookalike address into the user's transaction history before the others. Whoever succeeds first increases the chances that their address will later be copied.
The address below demonstrates the scale of this competition. In this case, 13 poison transfers were planted within a couple minutes of a legitimate USDT transfer.
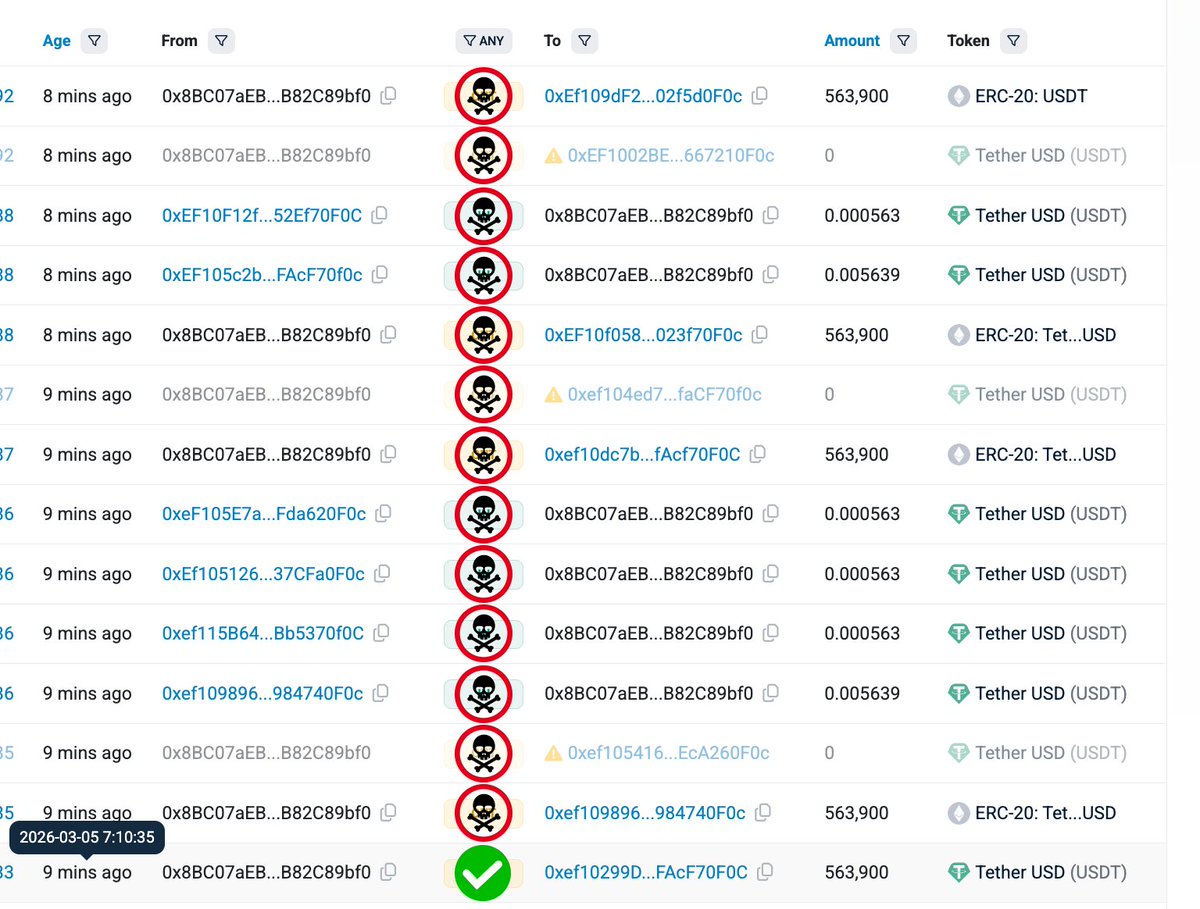
Note: Etherscan hides zero-value transfers by default; here they were unhidden for demo purposes.
The common tactics used in address poisoning attacks include
dust transfers,spoofed token transfers, and zero-value token transfers
2) Why These Attacks Are Easy to Run at Scale
At first glance, address poisoning may seem ineffective. After all, most users will not fall for the scam. But the economics of these attacks tell a different story.
A Numbers Game
Researchers found that a single poisoning attempt has a success rate of ~0.01% on Ethereum. In other words, only about 1 out of every 10,000 poisoning transfers results in a user mistakenly sending funds to the attacker.
Instead of targeting only a handful of addresses, poisoning campaigns often send thousands or even millions of poison transfers. When enough attempts are made, even a tiny success rate can generate significant profits.
A single successful attack involving a large transfer can easily cover the cost of thousands of failed attempts.

Lower Transaction Costs Encourage More Poisoning Attempts
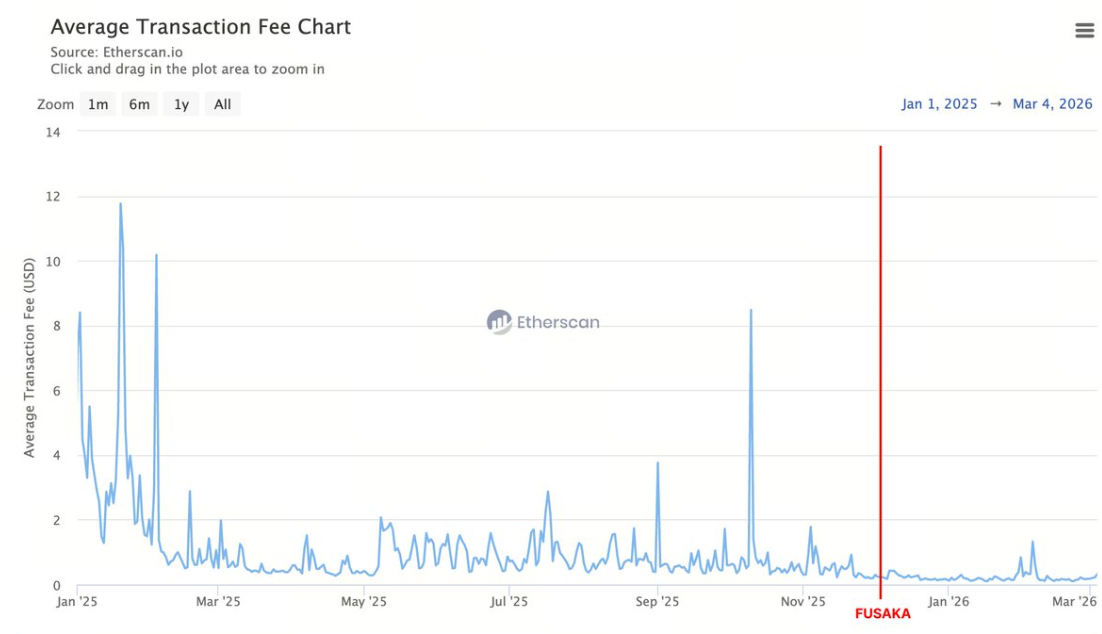
https://etherscan.io/chart/avg-txfee-usd
TheFusaka upgrade, activated on December 3, 2025, introduced scalability improvements that reduced transaction costs on Ethereum. While this benefits users and developers, it also lowers the cost of each poisoning transfer, allowing attackers to send far more poisoning attempts.
Network activity increased noticeably after Fusaka. In the 90 days following the upgrade, Ethereum processed on average 30% more transactions per day than in the 90 days before it. During the same period, the number of new addresses created each day increased by ~78% on average.
Besides, we observed a notable increase in dust transfer activity, where attackers send a very small amount of the same token a user has previously transferred.
The data below compares dust transfer activity across several major assets in the 90 days before and after the Fusaka upgrade. For stablecoins such as USDT, USDC, and DAI, dust transfers refer to amounts below $0.01. For ETH, they refer to transfers below 0.00001 ETH.
USDT Before:4.2M
After: 29.9M
Increase: +25.7M (+612%)
USDC Before: 2.6M
After: 14.9M
Increase: +12.3M (+473%)
DAI Before: 142,405
After: 811,029
Increase: +668,624 (+470%)
ETH Before:104.5M
After:
Increase: +65.2M (+62%)
Dust transfers (below $0.01) show a clear surge shortly after the Fusaka upgrade, with activity rising sharply before gradually tapering off while still remaining at an elevated level compared to pre-Fusaka levels. In contrast, transfers above $0.01 remain relatively stable throughout the same period.
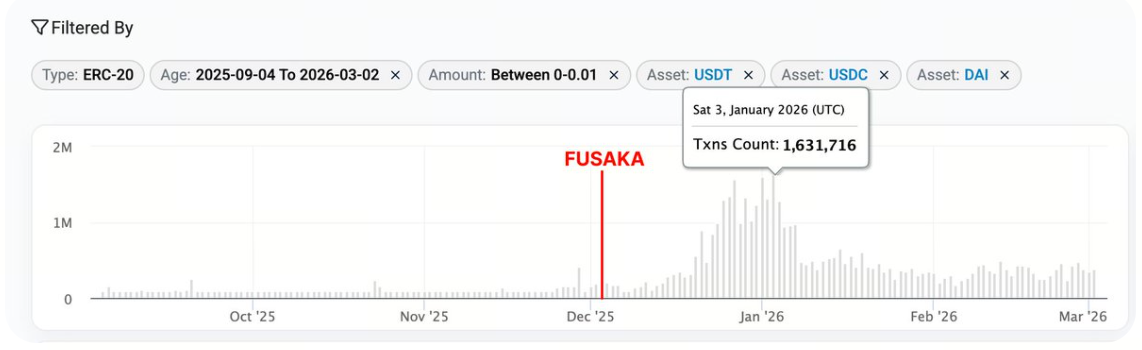
Screenshot: Dust transfers <$0.01 for USDT, USDC, and DAI in the 90 days before and after the Fusaka upgrade. (Source)
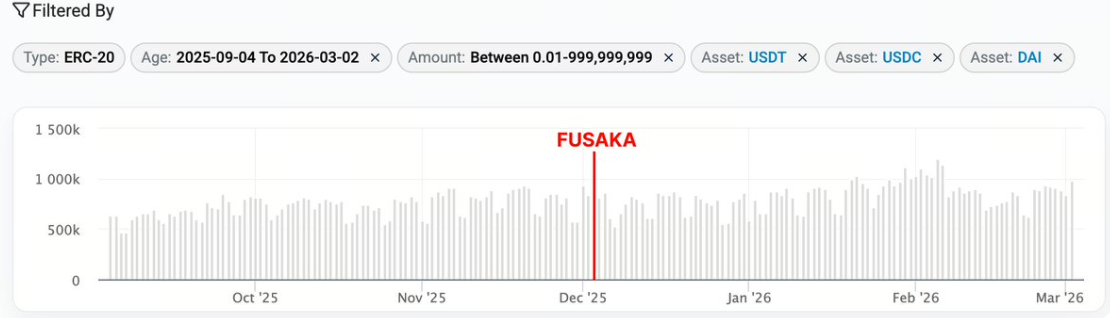
Screenshot: Transfers >$0.01 for USDT, USDC, and DAI in the 90 days before and after the Fusaka upgrade. (Source)
In many campaigns, attackers first mass-send tokens and ETH to newly generated spoofed addresses, which then forward dust transfers to the target address individually. Because dust transfers involve negligible token amounts, they can be executed cheaply and at scale as transaction costs decrease.
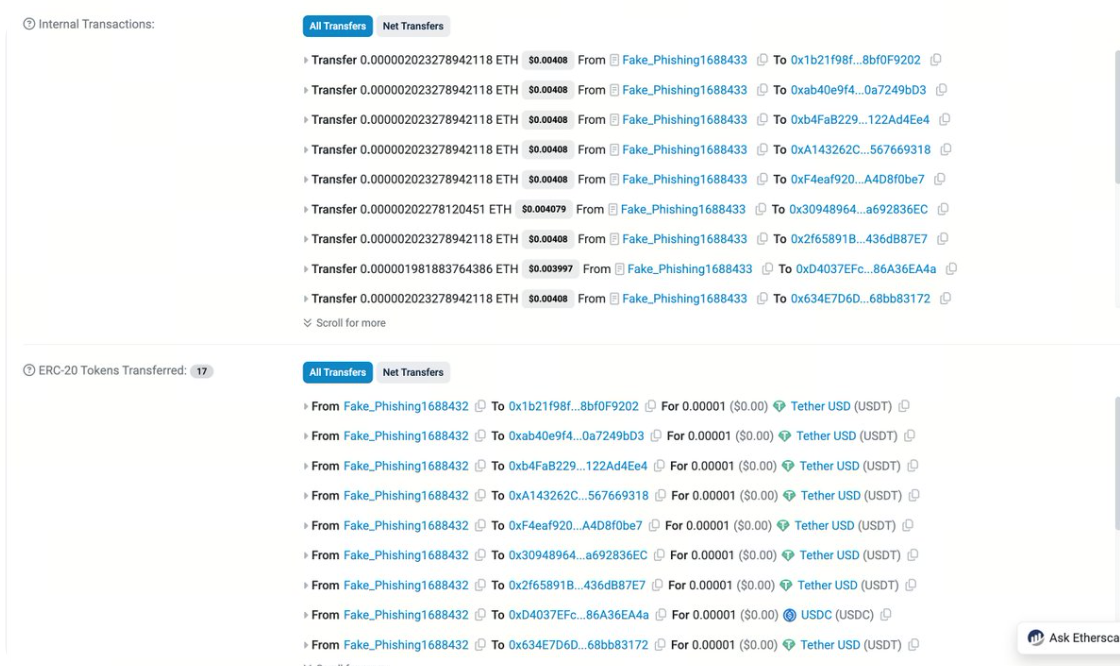
Screenshot: Fake_Phishing1688433 mass-sends tokens and ETH to different spoofing addresses in a single transaction. (Source)
It is important to note that not all dust transfers are poison transfers. Dust transfers can also occur as part of legitimate activity, such as token swaps or other small-value interactions between addresses. However, when reviewing dust transfer lists, a large portion of them appear likely to be poisoning attempts.
3) The One Rule to Remember
👉👉 Always verify the destination address before sending funds 👈👈
Here are a few tips to help reduce the risk when using Etherscan:
1. Make Your Addresses Recognizable
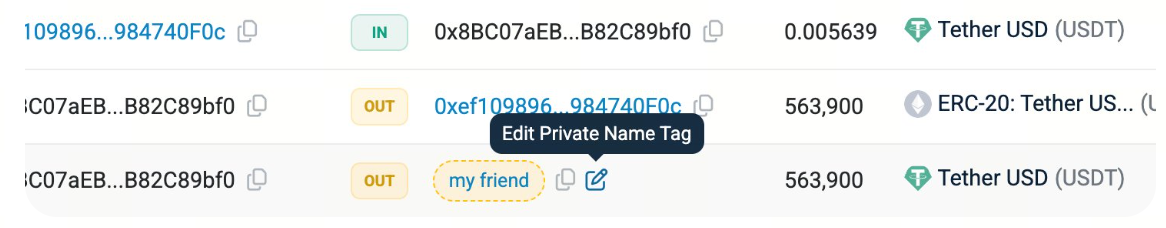
Use private name tags on Etherscan for addresses you frequently interact with. This helps legitimate addresses stand out clearly among lookalikes.
Using a domain name such as ENS can also make addresses easier to recognize across the explorer.
You should also use your wallet’s address book to whitelist frequently used addresses so you always know exactly where you are sending funds.
2. Use Address Highlighting
Etherscan’s Address Highlight feature helps you visually distinguish between similar-looking addresses. If two addresses look nearly identical but are not highlighted the same way, it is highly likely that one of them is an address poisoning attempt.
If you do not see this feature working, ensure it is enabled in Site Settings.
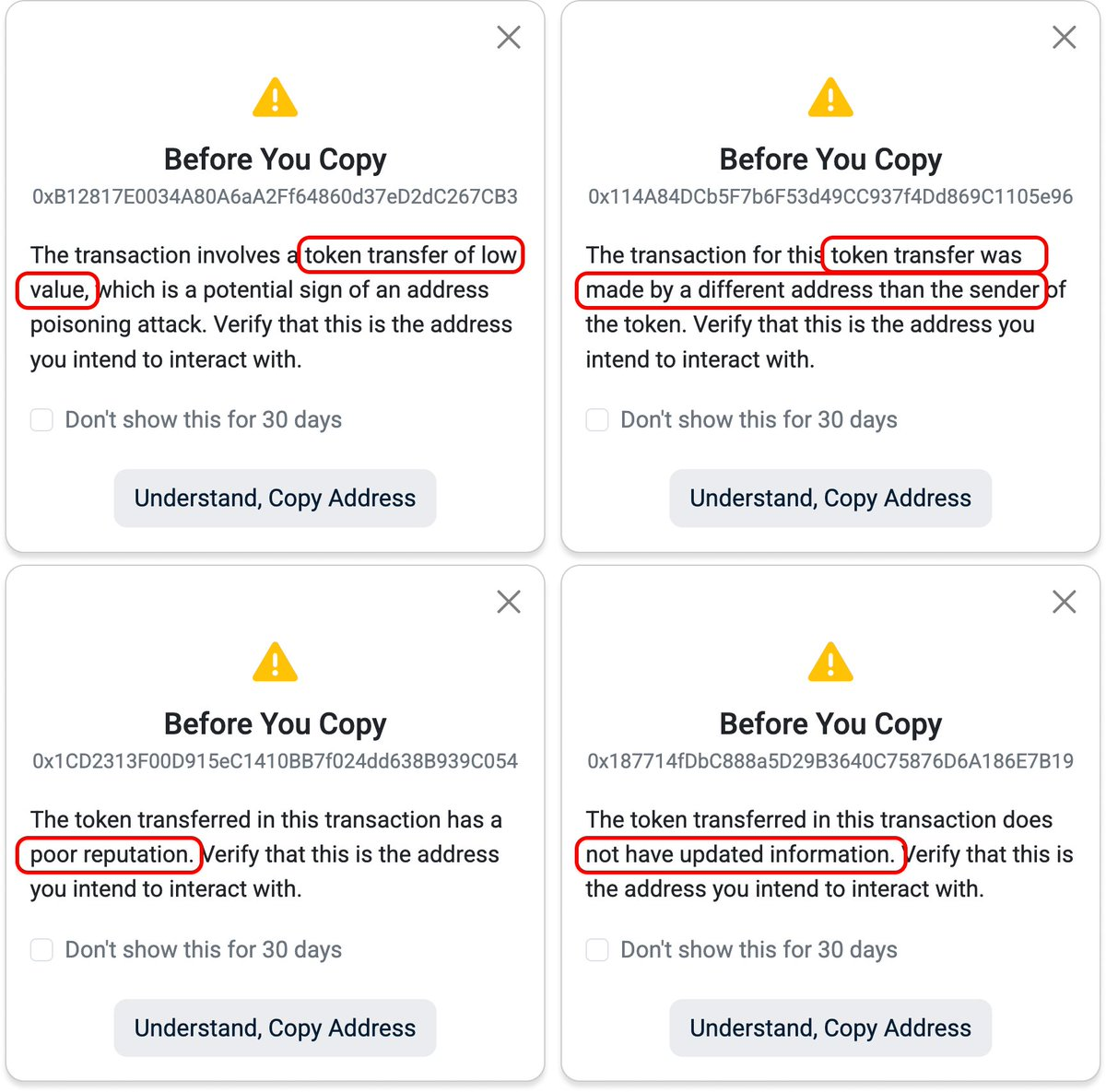
3. Always Double-Check Before Copying
Etherscan also provides popup reminders when copying addresses that might be associated with suspicious activity, including:
-
Low-value token transfers
-
Spoofed token transfers
-
Tokens with poor reputation
-
Tokens without updated info
When you see these reminders, take a moment to confirm that the address you are copying is the one you truly intend to interact with.
 If you would like a more comprehensive checklist to avoid these attacks, you can refer to our detailed guide here
If you would like a more comprehensive checklist to avoid these attacks, you can refer to our detailed guide here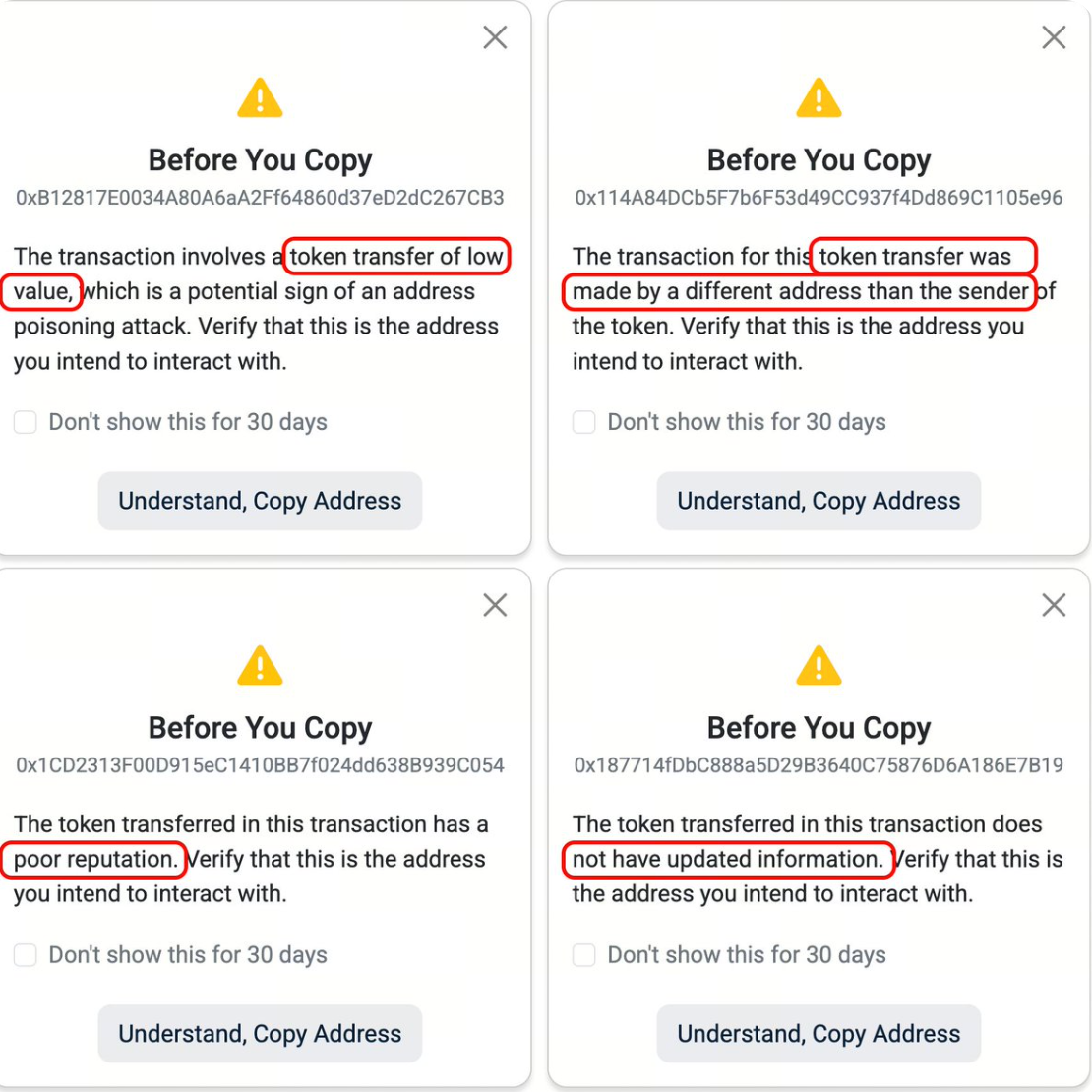 .
.
Remember, there are no undo buttons in crypto. If funds are sent to the wrong address, recovering them is extremely unlikely.
Final Thoughts
Address poisoning attacks appear to be becoming more prevalent on Ethereum, particularly as lower transaction costs make high-volume strategies cheaper to execute. These attacks also affect user experience, as transaction histories across many user-facing interfaces can become cluttered with poison transfer spam.
Protecting against these attacks requires both user awareness and better interface design. For users, the most important habit is simple: always verify the destination address carefully before sending funds.
At the same time, tools and interfaces can play an important role in helping users detect suspicious activity more quickly.
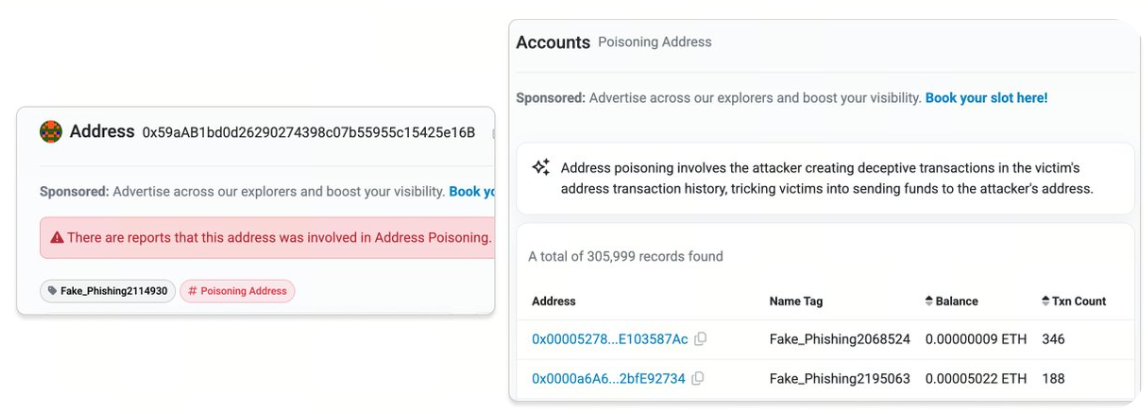
Poisoning Address labels on Etherscan (https://etherscan.io/accounts/label/poisoning-address)
At Etherscan, we continuously improve our explorer interfaces and API services to help users detect these attacks more easily. We actively label spoofing addresses, flag and hide zero-value token transfers, and tag spoofed tokens so our curated data can surface potential address poisoning attempts without users needing to manually sift through large volumes of transactions.
As poisoning campaigns scale through automation and high-volume dust transfers, surfacing these signals becomes increasingly important for helping users distinguish suspicious activity from legitimate transactions.
If you have any feedback or suggestions on how we can improve these protections further, feel free to reach out to us.
Disclaimer:
-
This article is reprinted from [etherscan]. All copyrights belong to the original author [etherscan]. If there are objections to this reprint, please contact the Gate Learn team, and they will handle it promptly.
-
Liability Disclaimer: The views and opinions expressed in this article are solely those of the author and do not constitute any investment advice.
-
Translations of the article into other languages are done by the Gate Learn team. Unless mentioned, copying, distributing, or plagiarizing the translated articles is prohibited.
Related Articles

What Is Ethereum 2.0? Understanding The Merge

Reflections on Ethereum Governance Following the 3074 Saga
Our Across Thesis

What is Neiro? All You Need to Know About NEIROETH in 2025

What is Polygon 2.0 (POL)? From MATIC to POL (2025)


